Security
Sandbox isolation, network controls, and the coSPEC security model
Sandbox Isolation
Every run gets its own gVisor sandbox. gVisor intercepts system calls at the kernel level, preventing the agent from accessing host resources or other tenants.
- No shared resources between runs or tenants
- Non-root execution, no privilege escalation
- Sandbox is destroyed after run completion
Network Access Control
All outbound traffic is blocked except explicitly allowed domains. The default allowlist covers git providers, the Anthropic API, and package registries.
Custom domains are configurable per template (up to 20). Private IP ranges (10.x, 172.16.x, 192.168.x, link-local) are always blocked.
See Templates — Network Access for the full default domain list.
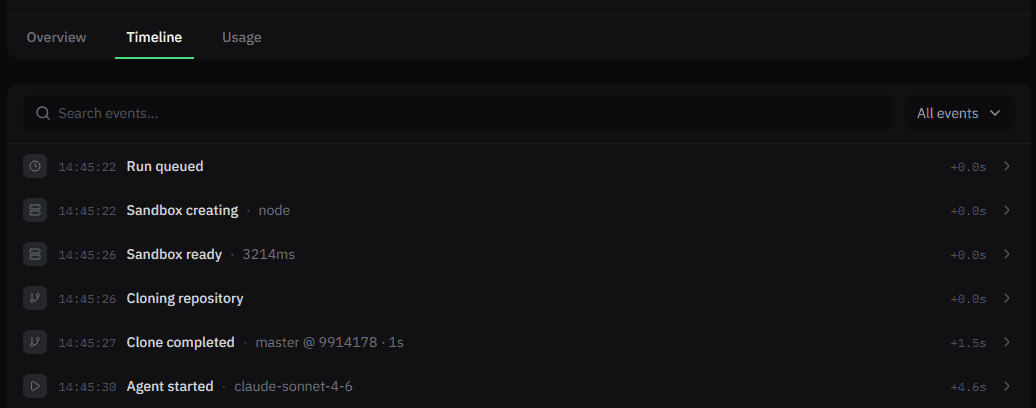
Audit Trail
Every run action is logged: sandbox creation, git clone, agent messages, tool calls, and errors.
Authentication
- API keys — prefixed (
csk_live_*), hashed and never stored in plaintext. See API Keys. - Dashboard — session-based with email verification and OAuth (Google, GitHub).
- Multi-factor authentication (MFA) — TOTP-based 2FA available for all accounts using email/password sign-in. Enable from Account Settings. Once enabled, a 6-digit code is required on every sign-in. Backup codes are provided at setup and can be regenerated at any time.
AI Security
Model Usage
We do not use your data to train any AI models.
The platform follows the BYOM (Bring Your Own Model) principle. You configure which models are used (e.g., Anthropic), while coSPEC handles orchestration, security controls, and execution.
Data and Privacy
Encryption in Transit
All communication with the platform is encrypted using HTTPS. With TLS 1.3 or TLS 1.2 enforced and modern cipher suites, we ensure secure communication between services.
Encryption at Rest
All persistent data stored by the platform is encrypted at rest. Databases, logs, and any other stored information are protected using strong encryption algorithms and secure key management practices.
Backup
Automated backups are performed regularly to ensure data durability. All backup data is encrypted and stored securely with controlled access.
Privacy
The system processes and stores operational data required to run agents and provide observability. This includes:
- Prompts and agent responses
- Execution logs
- Audit and system events
All stored data is encrypted and accessible only to authorized components of the platform.
Data Retention
Operational data is stored for a limited period to support debugging, observability, and auditability. The retention period could be agreed contractually based on customer needs. After the retention period, data is securely deleted from all storage systems.
Data Transparency
All data stored by the platform is available to the customer through logs and the dashboard. Customers have full visibility into what information is stored, how it is used, and can access or delete it as needed. You can see everything which is stored in the system, including prompts, logs, and execution history.
Infrastructure Security
The platform infrastructure runs on Google Cloud Platform (GCP) and follows strict access control policies. All access to production systems is protected by strong authentication mechanisms, and network access is restricted through firewall rules. The sandbox environments operate with limited OS-level permissions to minimize the risk of security breaches.
Production Database Access Control
Access to production datastores requires strong authentication. It is strictly limited to authorized personnel and services.
Secret Management
All secrets used by the platform are stored and managed through a dedicated secure secret management service. We do not hardcode any secrets in code or configuration files. Secrets are stored in a centralized vault with strict access controls, ensuring that only authorized components and personnel can access them.
Account Authentication
Access to internal systems and services requires individual user accounts. Access is granted based on role and business need, with no shared accounts allowed.